Our security solutions
Comprehensive cybersecurity solutions to protect your business from evolving threats and ensure complete peace of mind
In today’s digital landscape, cybersecurity threats are constantly evolving. Technocitta provides cutting-edge security solutions powered by AI and advanced threat intelligence to safeguard your network, endpoints, data, and cloud infrastructure against sophisticated attacks.
Network security
Protect your entire network infrastructure from external and internal threats with advanced firewall protection and intrusion detection systems.
Next-Generation Firewall (NGFW)
Intrusion Detection & Prevention
Network Traffic Analysis
VPN & Secure Remote Access
Network Segmentation
Endpoint security
Comprehensive protection for all devices connected to your network, including desktops, laptops, mobile devices, and IoT endpoints.
Advanced Anti-Malware & Anti-Virus
Endpoint Detection & Response (EDR)
Device Control & Management
Patch Management
Mobile Device Security
Data security & Encryption
Safeguard sensitive business data with robust encryption, data loss prevention, and access control mechanisms.
Data Loss Prevention (DLP)
End-to-End Encryption
Data Classification & Discovery
Database Security
Backup & Recovery Solutions
Cloud security
Protect your cloud infrastructure and workloads across public, private, and hybrid cloud environments.
Cloud Workload Protection
Cloud Access Security Broker (CASB)
Container & Kubernetes Security
Cloud Configuration Management
Multi-Cloud Security Posture
Threat Detection & Response
AI-powered threat detection with real-time monitoring, analysis, and automated incident response capabilities.
Security Information & Event Management (SIEM)
Extended Detection & Response (XDR)
Automated Threat Hunting
Behavioural Analytics (UEBA)
Security Orchestration (SOAR)
Email and application security
Comprehensive protection for email communications and business applications against phishing, malware, and unauthorised access.
Advanced Email Filtering
Anti-Phishing Protection
Application Firewall (WAF)
API Security
Zero Trust Network Access (ZTNA)
Key Features and benefits


Ai Powered Detection
Machine learning algorithms continuously analyze threats and adapt to new attack patterns, providing proactive defense against zero-day vulnerabilities.


Real time monitoring
24/7 continuous monitoring of your entire security infrastructure with instant alerts for suspicious activities and potential threats.

Automated response
Predefined security playbooks and automated incident response reduce reaction time and minimize potential damage from threats.
Meet regulatory requirements including GDPR, PCI DSS, HIPAA, SOX, and industry-specific compliance standards.
Compliance support




Cross environment protection
Consistent security posture across on-premises, cloud, hybrid, and multi-cloud environments with unified policies.


Access to certified security professionals for consultation, implementation, and ongoing managed security services.
Expert support
Our Security Implementation Process
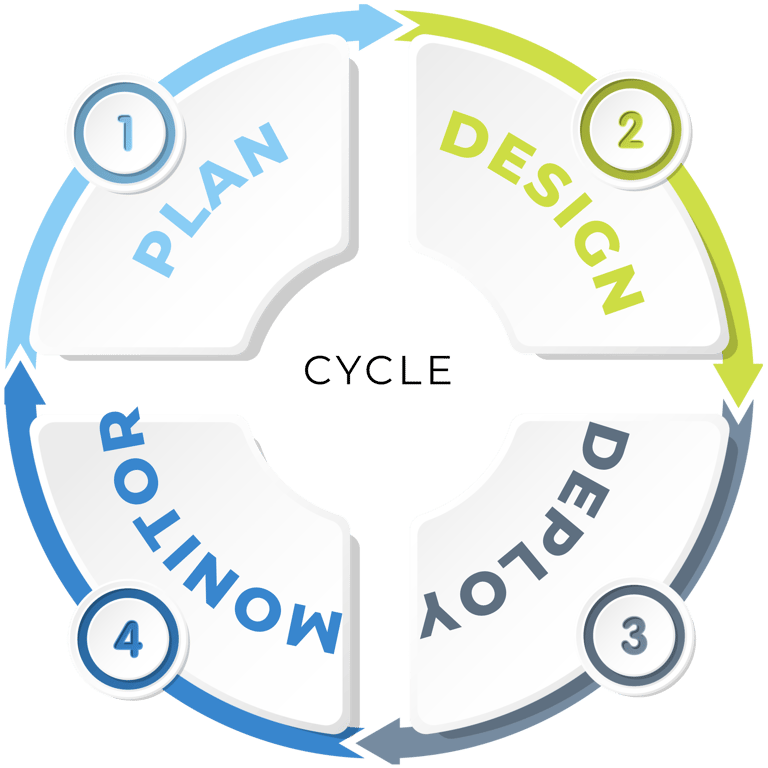
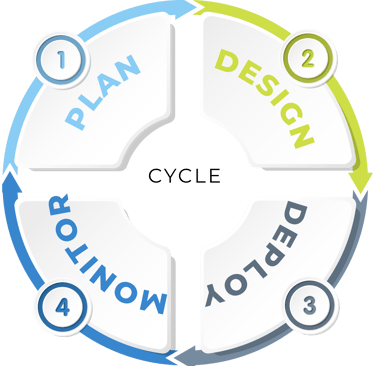
Assessment & Analysis
Comprehensive security audit to identify vulnerabilities, assess current infrastructure, and define security requirements.
Strategy Design
Develop customized security architecture aligned with your business goals, compliance needs, and risk profile.
Solution deployment
Expert implementation of security solutions with minimal disruption to business operations and comprehensive testing.
Continuous monitoring
24/7 threat monitoring, incident response, regular updates, and ongoing optimization to maintain robust security.
Technology partners






Get in touch
Join newsletter
© 2026. All rights reserved.
CIN No:U72900KA2020PTC14